May 17, 2018//-The boom of trials by some of the world’s largest banks, insurance companies and manufacturing businesses shows how the world is taking blockchain technology seriously.
While the breadth and depth of blockchain applications, trials and projects is expanding, there are relatively few examples of blockchain applications being used in everyday life, with many challenges to overcome ahead.
There are significant hurdles to blockchain technology adoption because it is complex and can be difficult to understand. There are hundreds of different implementations, as demonstrated by the proliferation of cryptocurrency and token networks.
As the evolution of Bitcoin has demonstrated, there are challenges to scalability, usability and transaction costs. There are debates in the blockchain community such as whether proof of work or proof of stake is preferable, or whether private blockchains are even part of the discussion.
Governance is also an issue; there is no central authority providing guidance on the right blockchain technologies nor does the implementation of blockchain technology negate existing regulatory conditions.
The massive amount of investment pumped into blockchain and distributed ledger technologies will accelerate innovation and evolution. In ten years, we may not recognize the commercial applications of blockchain technology, but they will have evolved from several of the key innovations pioneered by Bitcoin and the cryptocurrency space.
As the internet has demonstrated, one should not underestimate distributed networks that can host apps based on common code structures. The blockchain adventure has begun, and the race to the top is going to keep the blockchain technology industry and its partners in business for decades to come.
What is blockchain?
Blockchain technology enables the creation of secure, distributed ledgers driven by cryptography Blockchain has risen to prominence for managing transactions, especially in the cryptocurrency market.
The most known and discussed application of blockchain technology is used for the Bitcoin cryptocurrency, yet the technology has many other applications.
In fact, there are more than a thousand cryptocurrency and token networks as well as growing potential for use within a variety of vertical industries. Much of the excitement and speculation around blockchain and distributed ledger technology is tied to the ability to secure, manage and verify data in a tamperproof environment.
Individual transactions are encrypted using public-private key cryptography and verified by every node on the network. The built-in cryptography of blockchains allows transactions or objects to be tracked without the need for a third party and enables a secure, distributed database of transaction data that is instantly verifiable by the community.
This approach has the potential to replace traditional database or escrow approaches and could revolutionize industries that require high data security and integrity, such as the financial, medical, information technology (IT), manufacturing and government verticals.
There are, however, also many challenges, including scalability and cost. Read on to see how blockchain technology could change the way industries manage transaction data and contracts, discover real-world implementation challenges, and see how this business model could impact our world in the long-term.
Blockchain replaces gatekeepers, middlemen and record-keepers with a more secure, automated and distributed system The key characteristics of blockchain are attractive to many industries, governments and organizations.
Bitcoin is a strong example of how blockchain infrastructure and technical elements operate. The technology used to record and store transactions for Bitcoin is applicable to a variety of industries outside of this specific market.
THE TECNOLOGY BEHIND BITCOIN
A deep dive into Bitcoin is helpful in illuminating the blockchain technology infrastructure:
– Embedded cryptography – Bitcoin blockchain technology automatically integrates public- and private-key cryptography as a default. This means that all transactions are natively encrypted with public and private keys.
To unlock a particular transaction or “smart contract” on a blockchain, one would need to apply a specific private key to the public address. The public address encrypts the data so that it can only be unlocked with that specific private key.
– Secure blocks – There are variations in the approach of various blockchain technologies, but they all work on the same premise of grouping data in a tamper-proof chain; as records are verified by the network members, they are added in blocks to the block chain. Each record or transaction must be verified by the community.
– Proof of work verification – The most common approach to verification is “proof of work.” The data is run through a cryptographic puzzle, which contributors to the network are asked to verify by solving. This requires sufficient computing power to decode the puzzle, hence the proof of work.
–Transaction payments – Incentives are required to add transactions to a blockchain. The participants— known as “miners” in the Bitcoin network—are rewarded with Bitcoins for their work.
– Network data security and integrity – Once the data is added to the blockchain, it is encrypted with a unique hash then copied to all of the nodes on the system. These transactions are linked by a hash generated by the prior transaction of the blockchain.
This means that if someone tries to alter the transaction, it alters the data in the entire blockchain down the line and is instantly recognized as fraudulent.
– Peer to peer – The data in a blockchain is copied to “hosts” or “peers.” The peer-to-peer, distributed nature of blockchain technology makes data instantly verifiable and difficult, if not impossible, to tamper with. As soon as one copy is altered, the rest of the network knows the data has been compromised.
Hashing is crucial
Hashing, the process of encrypting transaction data, is used both for proof of work as well as locking blocks into the blockchain with a unique signature that cannot be altered.
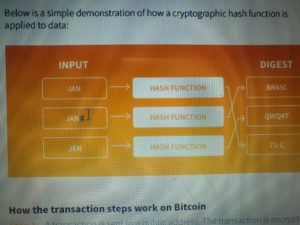
When cryptographic function is applied to a string of data, the output is an unrecognizable code. If one letter in the code is altered, the output will be radically different, making alterations instantly identifiable.
This, combined with integrated public- and private-key cryptography, is what makes the blockchain unique. It is relatively easy to “hash,” or sign, the data, creating the output.
Yet it is very difficult to recognize the original message by looking at the output data or “digest” of the hash, as shown in the diagram below. If even one character or binary digit is changed in the input data, the hash function will render a completely different output, therefore recognizing tampered data.
Below is a simple demonstration of how a cryptographic hash function is applied to data:
How the transaction steps work on Bitcoin
Step 1 – A transaction is sent to a public address. The transaction is encrypted using a public and private key, which must be used simultaneously. Like a private message locked inside a locked mailbox, the owner must have both the mailbox key and the message key.
Step 2 – The encrypted data is “hashed” (signed with cryptography) and broadcast to members who must use computing power to decode the hash to verify the data.
Step 3 – Once the transaction is verified, it is approved and added as a “block” of data to the blockchain. This copy is then sent to the nodes of the network. Each new block is applied with a hash from the prior block, meaning data cannot be altered once it is added to the blockchain.
Step 4 – All data is timestamped to prevent duplicate transaction attempts.
Curled from IHS Markit’s ebook titled: Blockchain Technology, Use Cases and Challenges